Originally published by me at: https://www.todayslegalcyberrisk.co.uk/guest-writers/email-security-are-you-giving-away-your-personal-information/
Smart Phones. You carry this with you every day, have you ever stopped and wondered what kind of information it holds? Or how much information about you it holds? Let me put this simple, your phone knows more about you than you may know about yourself.
In my line of work, there is no such thing as “I am fully protected”. So, the only way to make sure you are safe is, to take some precautionary measures.
Here are a few things you need to be aware of about the minuscule device you carry around and engage, along with few tips:
Passwords:
It’s something that has become a necessity in this modern world and is not tied to a single source. We login into multiple websites all the time. Due to the number of times and the count of websites, we tend to use either the same passwords, save it for easier access or use the “Save your password” option that your web browser provides.
Yes, it sounds easier, but imagine someone compromising your email account which gives them access to all the passwords you’ve been saving.
Solution:
Do not save passwords in your browser. Use password vaults to store them. This way only a master key needs to be remembered and make sure it meets strong password requirements.
With my personal experience, I recommend using LastPass to store your passwords. LastPass even supports a plugin system as well, which is easier to use when you are browsing and need to log into a website.
Sensitive documents, Text messages:
We all access documents on our mobile on daily basis, I am not going to suggest avoiding downloading or accessing sensitive documents on your phone, such as bank statements, tax documents, storing credit card numbers on autofill etc.
Delete them after you use as well as any text that might hold sensitive information and refrain saving credit card information, addresses as autofill on your browser.
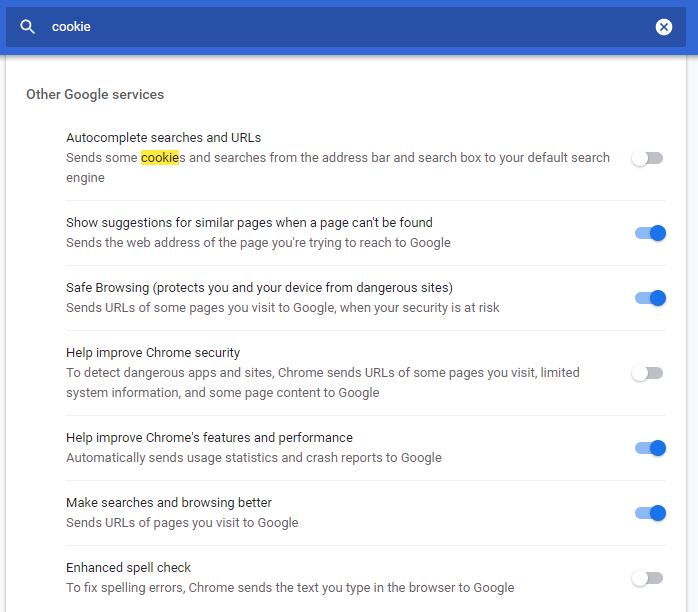
Cookies and whatnots:
Cookies are not harmful like malware, worms or viruses. But have you speculated how you get suggestions in Facebook on what you were searching before. Well! This is how, cookies track your browsing data and end up displaying customized advertisements. It’s a threat to your anonymity and also questions your privacy.
Want more control over what Google knows about you? Here is one of my articles explaining it – click here.
Solution:
- You can turn off cookies under browser settings or you can always use this amazing plug-in called Ghostery. Ghostery is an excellent browser extension that will help you with safe browsing by blocking tracking technologies.
- Clear off browser history, cache once every week (doing it every day would be a tedious job).
Deleted files:
When you are done with your phone or even a computer/laptop for that matter, you tend to either throw it away, sell to someone or to a store as a used product. Here is a shocker, did you know that the files you deleted are never really gone? It can always be recovered.
This also includes when you delete the files and move it to trash or recycling bin.
Solution:
The one and only solution, rewrite physical storage with something unnecessary or zeroes so that space can be overwritten.
Here’s what happen when you delete a file, the space is simply freed up and according to the computer/system, the file is no longer present on the hard drive and the space is free to use. Until that space is overwritten by something else, the files allocated earlier could still be recovered.
There are a lot of file shredding tools available online which can, not only be used to permanently erase data but also the data is overwritten that prevents recovery of the deleted files.
Tool you can use: Ghostery (Windows), DoYourData (MAC)
App Permissions:
Saved the best for last.
Who doesn’t love to try a new trending App on their phone? Isn’t easy? Click, click and install…and bada-boom, you have the app on your phone. Here’s what something you might not be aware of. Most of the apps have access to data that’s unnecessary for the app to function.
App developers do let you know the access they need but are sneaky about it, and we are in a hurry in installing them, we fail to check.
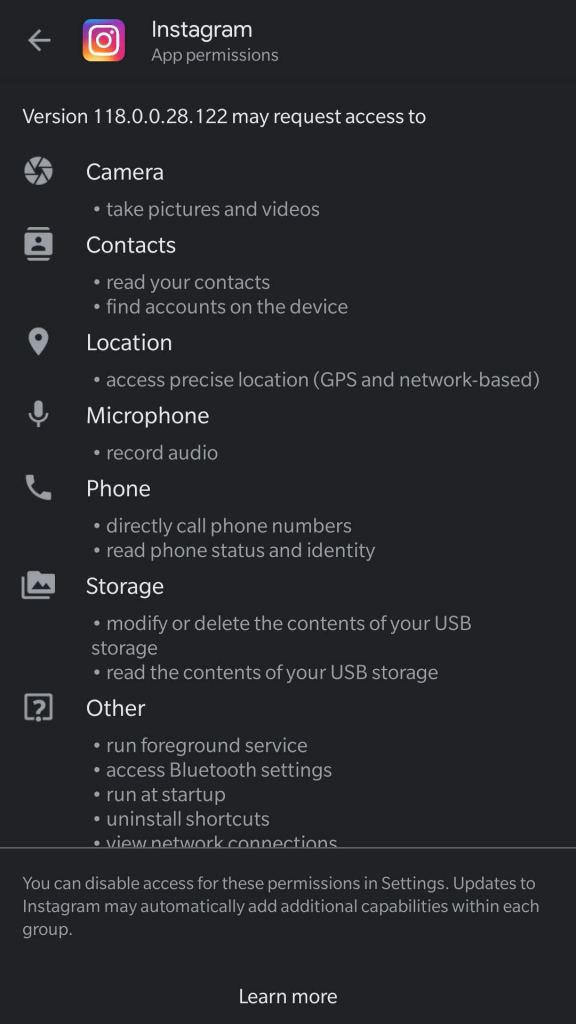
For instance, take Instagram,
(Android) Navigate to the app on Play Store, go to “About this app” -> Scroll down to “App permission” to “See More”
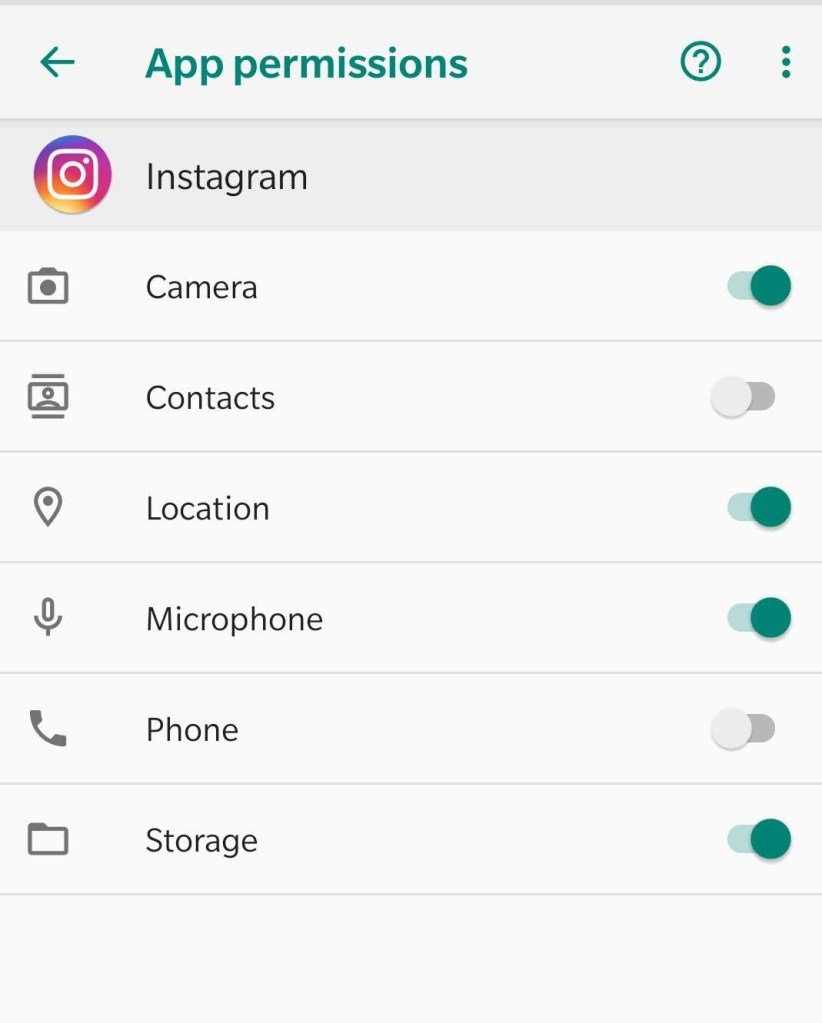
This will give you the access that the app might use. Appalled? That’s alright, if you feel like it’s an unnecessary access, you can always turn it off.
Here is how:
Under App Settings on your phone. (Settings -> Apps & Notifications -> [Choose your App] -> Permission -> Choose which ones you want to allow.
Reading through the whole article might make you think, why go through this? What a hacker is going to do with my data/information?
You know the saying “Information is wealth?” In cybersecurity, that’s what makes you rich. Nothing else. So, keep your information secure. Stay safe and sound!


